Intel tried desperately in
a press note late Wednesday to brush aside allegations that the recent
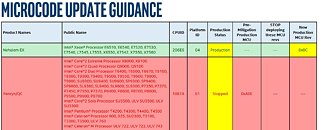
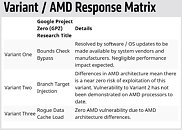
hardware security-vulnerability are a "bug" or a "flaw," and that the media is exaggerating the issue, notwithstanding the facts that the vulnerability only affects Intel x86 processors and
not AMD x86 processors (despite the attempt to make it appear in the press-release as if the vulnerability is widespread among other CPU vendors such as AMD and ARM by simply throwing their brand names into the text); notwithstanding the fact that Intel, Linux kernel lead developers with questionable intentions, and other OS vendors such as Microsoft are keeping their correspondence under embargoes and their Linux kernel update mechanism is less than transparent; notwithstanding the fact that Intel shares
are on a slump at the expense of AMD and NVIDIA shares, and CEO Brian Kraznich
sold a lot of Intel stock while Intel was secretly firefighting this issue.
The exploits, titled "Meltdown," is rather glaring to be a simple vulnerability, and is described by the people who discovered it, as a bug. Apparently, it lets software running on one virtual machine (VM) access data of another VM, which hits at the very foundations of cloud-computing (integrity and security of virtual machines), and keeps customers wanting cost-effective cloud services at bay. It critically affects the very business models of Amazon, Google, Microsoft, and Alibaba, some of the world's largest cloud computing providers; and strikes at the economics of choosing Intel processors over AMD, in cloud-computing data centers, since the software patches that mitigate the vulnerability, if
implemented ethically, significantly reduce performance of machines running Intel processors and not machines running AMD processors (that don't require the patch in the first place). You can read Intel's goalpost-shifting masterpiece after the break.