Thursday, January 4th 2018

Intel Released "Coffee Lake" Knowing it Was Vulnerable to Spectre and Meltdown
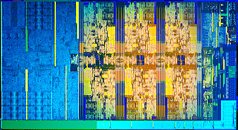
By the time Intel launched its 8th generation Core "Coffee Lake" desktop processor family (September 25, 2017, with October 5 availability), the company was fully aware that the product it is releasing was vulnerable to the three vulnerabilities plaguing its processors today, the two more publicized of which, are "Spectre" and "Meltdown." Google Project Zero teams published their findings on three key vulnerabilities, Spectre (CVE-2017-5753 and CVE-2017-5715); and Meltdown (CVE-2017-5754) in mid-2017, shared with hardware manufacturers under embargo; well before Intel launched "Coffee Lake." Their findings were made public on January 3, 2018.
Intel's engineers would have had sufficient time to understand the severity of the vulnerability, as "Coffee Lake" is essentially the same micro-architecture as "Kaby Lake" and "Skylake." As one security researcher puts it, this could affect Intel's liability when 8th generation Core processor customers decide on a class-action lawsuit. As if that wasn't worse, "Skylake" and later micro-architectures could require micro-code updates in addition to OS kernel patches to work around the vulnerabilities. The three micro-architectures are expected to face a performance-hit, despite Intel extracting colorful statements from its main cloud-computing customers that performance isn't affected "in the real-world." The company was also well aware of Spectre and Meltdown before its CEO dumped $22 million in company stock and options (while investors and the SEC were unaware of the vulnerabilities).
Intel's engineers would have had sufficient time to understand the severity of the vulnerability, as "Coffee Lake" is essentially the same micro-architecture as "Kaby Lake" and "Skylake." As one security researcher puts it, this could affect Intel's liability when 8th generation Core processor customers decide on a class-action lawsuit. As if that wasn't worse, "Skylake" and later micro-architectures could require micro-code updates in addition to OS kernel patches to work around the vulnerabilities. The three micro-architectures are expected to face a performance-hit, despite Intel extracting colorful statements from its main cloud-computing customers that performance isn't affected "in the real-world." The company was also well aware of Spectre and Meltdown before its CEO dumped $22 million in company stock and options (while investors and the SEC were unaware of the vulnerabilities).
111 Comments on Intel Released "Coffee Lake" Knowing it Was Vulnerable to Spectre and Meltdown
Oh well. Keep On Digging
Meltdown affects ALL INTEL CPUS THAT SUPPORT Out Of Order Execution which is pretty much all Intel CPUs released since 1995 other then some Atom and all Itanium CPUs.
Spectre is a different story though. Spectre potentially allows a program to access memory from another running program. This could potentially allow the program to steal things like your credentials, browser history, credit card numbers, and so on.
So, yes, if you are running a modern Intel CPU then you need the OS update. And you will also need the BIOS update to fix the ME exploit which allows malicious programs to get beyond kernel level access to a Intel based machine.The Intel CEO may still run into issues with insider trading if he did not have the share sale time and quantity predetermined before Intel found out about the vulnerabilities.
Anyway...
Coffee lake was meant to be a release of 6 core cpus with no architectural changes.
There would be no point in halting the release of coffee lake, especially when ES/QS cpus are being provided, and all partners already have working prototypes of new platform.
As the OS workaround is already out, the problem is resolved. Not in a way satisfying everyone, but it is resolved.
So the truth is Intel never worried about AMD; they worried about their own disastrous mistakes tanking a launch that might have otherwise been great for them. It's really hard to believe the entire tech industry tried to protect Intel from its own shortsightedness rather than expose them and let them reap all that they sowed.
AMD did not know about Spectre from their behavior until the project zero release, is my bet. Otherwise they would not have tried to market their cpus as immune in a rather vain struggle.
Intel WAS a quality company back in the 386/486/586 days. Their CPU's where superior compared to cloned ones such as AMD. But from that complete P3 and above, alot of various tactics where used to put themself on top and keep it that way, by offering vendors huge discounts of not the competition (=AMD) was being sold to the mass.
This company should burn over this case.
This vulnerability has your computer completely exposed to attacks that you don't even comprehend yet. Oh and not having antivirus is an excellent recipe where you are already breached and someone might using your system for DDOS attacks or someone might be threatening someone pretending to be you. Things can go bad to worst and you won't even know it until authorities show up at your doorsteps.
CPUs are already designed, probably even the next Intel release will still contain the same architecture with the same leak.
This topic and the supposed scandal of Intel stock being sold are perfect examples of everything we don't really need. Only Meltdown is directly attributable to an Intel specific design, Spectre hits everyone. Also consider the alternative: not releasing anything, not just for the past 6 months but also the next year. Meanwhile, you also can't disclose WHY you're not releasing anything. Imagine the question marks that would raise...
The fact that Intel is a rat company was known long ago, these news items really add zero to that fact.
You guys are acting like right now everyone with a personal computer is at risk while surfing the web and is the end of the world. This affects big data centers and companies more than anything, not the home user. Most of those exploits can´t even be used against you, unless you use specific apps/tasks. And as I said, it is fixed now, so chill out. Intel is still faster than Ryzen, and that still makes more money to some people, wich is what matters.
In addition, as I posted earlier to clarify, EVERY SYSTEM is vulnerable. Including your home PC. Happen to be a crypto whale? I'd start worrying.
- Entry: have code execution on system = ridiculously easy. Any website can inject malware, remember the malware we got served by ads not too long ago?
- Method: uses a very basic processor function that is present everywhere. Any attack is potentially huge in scope
- Impact: Read out memory and you can spy on everything someone does on a rig
- Action: software patching. As with all software, it can be hacked.
Let me sketch a worst-case scenario: software patching keeps getting circumvented and new hacks actually occur using these backdoors. At some point, public outrage forces Intel/AMD to start disabling branch prediction/speculative exec entirely. All of a sudden we're back in Sandy Bridge performance metrics ie. performance drops to 2012 mainstream.
newsroom.intel.com/news-releases/industry-testing-shows-recently-released-security-updates-not-impacting-performance-real-world-deployments/
The company should burn if they would bail out on their customer base ... which mind you Intel isn't going to do with the branch that provides the biggest chunk of their income (Data Centers).
Stop spreading misinformation if you guys don´t know what you´re talking about.
Bottom line: we now all own a system with a broken lock on one of the doors. The software patch allows us to put duct tape over it, so we can pray it holds until this gets an architectural fix.
googleprojectzero.blogspot.com/2018/01/reading-privileged-memory-with-side.html
Plus, older Intel designs were also full of issues, including the well known FDIV. It's even more significant when you think how far we've come in CPU design.
Also, your approach to this matter is really sad. Intel is the company running global microprocessor business. It's way more complicated than just you replacing your i7 with a Ryzen for gaming.
This problem might cost Intel billions and will have a serious impact on the whole computer industry.
That said, people are likely to be able to easily be tricked into running virus programs. If there weren't people that run random things, I probably would lose half my business, and all those ransomware people wouldn't be making any money. But at the same time, I'd bet any good anti-virus programs will very quickly be updated to watch for behavior of this exploit and stop it, I mean that is what anti-viruses do with minimal performance impact.
I'm just glad Intel did this, because now I'll get some money back from the class-action lawsuit!
The user really doesn't have to be in play here.
I am glad I took a seat on the sidelines here... this is humorous to watch what many believe/think they know/don't know... etc. and the reactions from some are priceless.
Not saying I know any better. I don't really, but I'm not here running around like a chicken with my head cut off. Life is good.